Even as they rise in popularity, smart home devices continue to pose some serious security risks. These are typically easy pickings for hackers who target these devices to access your personal information, spy on your activities, or cause damage to your home.
The dangers of smart home devices all too often fly under most homeowners’ radar. Seventy-five percent of people feel some level of distrust about the use of their data. Yet, as Alexis Curis of ‘Today’s Homeowner’ cites: the use of smart home technology continues its dramatic rise.
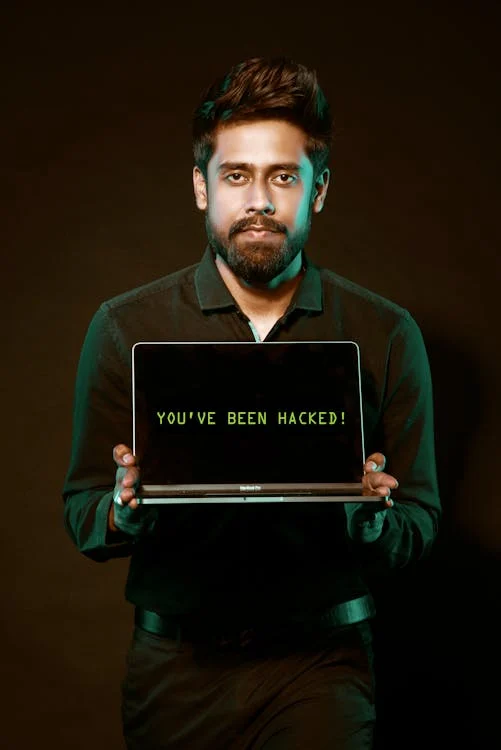
Even as ‘smart living’ makes things ultra-convenient, it's crucial to be vigilant about cyber threats. A hacker may have compromised your smart system without you even knowing it.
How to tell if a hacker has compromised your smart home device? Here are some signs to look out for:
1) Unexpected Behavior
Unexpected behavior doesn’t have to be as serious as HAL 9000 refusing to open the pod bay door for Dave in ‘2001: A Space Odyssey,’ but it should be disconcerting. It’s the first sign that someone has compromised your smart home device. If your device starts acting erratically, it's time to investigate. Erratic behavior can include:
Lights flickering
Thermostat settings changing
Smart locks behaving in an unpredictable manner
Hackers can create disturbances by manipulating smart devices. Noticing these irregularities early can prevent further damage.
2) Unusual Network Traffic
One fundamental aspect of home cybersecurity is monitoring your home network. Have you observed a sudden surge in data usage? Is your hard drive filling up too fast? Have you noticed unusual patterns in network traffic? If so, these could indicate unauthorized access.
There are two prime reasons why hackers may exploit your smart devices: to launch attacks like Ransomware or steal your sensitive information. Regularly check your router's activity logs. This helps you stay vigilant against abnormal network behavior.
3) Strange Sounds or Voices
Pay attention to Alexa! Smart speakers and voice-activated assistants are fairly commonplace in today’s households. It's a huge red flag if you start hearing unfamiliar voices or strange sounds from these devices.
Ensure that your smart devices are only responding to authorized voices, because hackers may use compromised devices to eavesdrop or communicate with household members. This poses serious privacy concerns.
4) Device Settings Modification
Have some device settings changed? They are not supposed to do that on their own. Smart devices offer customizable settings to cater to individual preferences. If you have noticed unauthorized changes to these settings - such as alterations in camera angles, sensor sensitivity, or device preferences, there's a high likelihood that a hacker has compromised your device.
Review and update your device settings regularly. This will help you maintain control over your smart home ecosystem.
5) Mysterious Data Transfers
One function of many smart devices is to collect and send data to the cloud for analysis or storage. Keep an eye on your device's data usage. Be wary of unexplained data transfers. Hackers may be exploiting vulnerabilities to extract sensitive information from your devices.
Review the data usage patterns of your smart devices regularly. This will help you to identify any suspicious activity and take action.
6) Device Inaccessibility
If you suddenly find that you’re locked out of your smart home devices, it could be a sign of hacking. Hackers may get in and change your passwords or enable two-factor authentication without your consent. They can take control of your accounts, rendering you unable to access or manage your devices.
Never put off addressing these anomalies – do it immediately. If a hacker has a foothold in your smart devices, it will only get worse. Secure your accounts if you suspect unauthorized access.
7) New or Unknown Devices on the Network
Review the list of devices connected to your home network regularly. If you spot unfamiliar or unauthorized devices, it’s a clear sign that someone may have breached your network.
To exploit vulnerabilities in smart devices or launch attacks, hackers often connect to your network. Make sure to secure your network with strong passwords. Also, consider implementing network segmentation and enhanced authentications like 2F (Two Factor) or MFA (Multi-Factor Authentication) for added protection.
8) Frequent Software Glitches
Due to their connected status, smart devices receive regular software updates that patch vulnerabilities and enhance security. Have you noticed frequent software glitches? Or has your device failed to update? It could be a sign of interference by a malicious actor.
Make certain that your smart devices are running the latest firmware. This will ensure that it has the latest security patches and bug fixes installed.
9) Emails or Messages Confirming Changes You Didn't Make
Some smart devices send notifications or emails to confirm changes in things like settings, passwords, or device access. If you receive a confirmation for an action you didn't take, this is a clear sign of unauthorized access.
Take immediate action to secure your account. This includes changing passwords and reviewing access permissions.
Frequently Asked Questions
What are the most vulnerable smart home devices?
According to Kaspersky, the most vulnerable “might include smart speakers, your internet router, your computer and your smartphone. Your smartphone, if hacked or stolen, could compromise your entire home security system, so make securing it your top priority by purchasing Android security or security for iOS devices.”
How do I stop Alexa from spying on me?
When turned on, Alexa is constantly listening for its own name and other voice cues. When you want Alexa to stay out of your business, press the mute button on any Echo device to turn off the microphone. A red light will display signaling that the microphone is disabled, and Alexa won't be able to eavesdrop or record anything you say – and transmit what you said back to Amazon (because it does).
What are the problems with AI in smart homes?
Good luck finding a definitive list, since new ‘wrinkles’ appear as quickly as old ones are fixed or patched. Some of the challenges include security and privacy concerns, data collection and sharing, data analytics, and latency.
There is also an unfulfilled need for explainable AI (XAI) solutions to improve user experience and trust by providing clear and understandable explanations of the system's behavior. Device manufacturers pitch what the device will do, not why it does what it does.
What does 2FA mean?
2FA is a two-factor authentication system - a security enhancement that requires two separate, distinct forms of identification in order to access something. The first factor is usually a password, and the second most common factor is a code sent to your smartphone which you enter during your login. Biometrics are also becoming more commonplace: using fingerprint, retina, or facial recognition.
How secure is your network?
As a reputable member of the IT Support Los Angeles community since 2002, IT Support LA offers a FREE, no-risk network and cybersecurity assessment. It is a non-intrusive scan that allows us to deliver a comprehensive report that is yours to keep. No strings, and no obligation to ever use our Managed IT Services.
The best defenses are expert Cybersecurity to protect your data from theft, and a top-notch Managed Services Provider to ensure continued reliability and defenses against newly emerging threats.
With our 100% Money Back Guarantee in writing, we offer a risk-free way for prospective clients to try us out. Because we do not require a ‘hard’ contract, our clients can fire us at any time with 30 days’ notice. We have to be good.
Among the Managed IT services we provide:
IT HelpDesk Service
Onsite IT Support
Cybersecurity
Cloud migration and management
Email migration services
Backup and disaster recovery
VoIP phone systems
IT disposition and recycling
Office moves
White label services (IT to IT)
IT Support LA is an award-winning Managed Services Provider (MSP):
o 3 Years awarded Best IT by the Small Business Expo
o Awarded 2nd best company of any type in the US by the Small Business Expo SB100
o Awarded Best IT in California by Channel Futures
o Winner of Best IT in Los Angeles by Channel Futures
o Listed as one of the world’s Top 501 Managed Services Providers by CRN and in the top 250 in the ‘Pioneer’ listing
o 4 years listed as one of the Top 501 Managed Services Providers in the World by Channel Futures
o Listed as #21 MSP in the World in Channel Futures NextGen 101
o Globee 2021 Bronze Award winner for Chief Technology Officer of the Year
o Globee 2022 Gold Award winner for Chief Technology Officer of the Year
o Named one of 2022’s 50 ‘Best’ businesses in California by UpCity
o Named one of 2023’s 50 ‘Best’ businesses in California by UpCity
o Named Best of IT Services winner by UpCity
o Winner of Local Excellence Award for 2021, 2022 and 2023 by UpCity
o Named Best of Cloud Consulting winner by UpCity
o Certified as Top Managed Services Provider and Cybersecurity Pro by UpCity
o Named Best IT Support in Los Angeles by Expertise.com.
Be Proactive About Cybersecurity – Schedule an Assessment
It's clear that the security landscape will continue to evolve rapidly. Organizations and individuals must proactively prepare for emerging threats. This includes adopting advanced technologies and prioritizing workforce development as well as staying abreast of regulatory changes.
Put a comprehensive network security strategy in place. One that encompasses these predictions. This will help you navigate the digital frontier with resilience and vigilance.
Need help ensuring a secure and trustworthy digital environment for years to come? Contact us today to schedule a network and security assessment.
818-805-0909