BOOM!
Boom. Okay, just what does that mean? As with many phrases, it comes from the military. ‘Boom’ is a negative event, like a bomb going off. Left of Boom are preventive measures, and Right of Boom are recovery measures.
For our purposes, BOOM represents a cyber-attack like Ransomware or a data breach. How do you prevent it, but if it does happen, how do you recover?
Every click and keystroke we make echoes through cyberspace in our highly digitized environment. The battle for data security is never over. Businesses stand as both guardians and targets while unseen adversaries covet their digital assets.
Navigating this treacherous terrain takes a two-pronged approach. Businesses must arm themselves with a sophisticated arsenal of Cybersecurity strategies. On one side, the vigilant guards of prevention (Left of Boom). On the other, the resilient bulwarks of recovery (Right of Boom).
Together, these strategies form the linchpin of a comprehensive defense. They help ensure that businesses can repel attacks and rise stronger from the ashes if breached.
Let’s look at how best to organize your Cybersecurity approach into Left and Right of Boom.
What is the left and right of boom in cyber security?
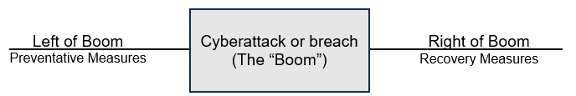
"Left of Boom" refers to preemptive measures and preventative strategies. These are things implemented to safeguard against potential security breaches. It encompasses actions aimed at preventing cyber incidents before they occur.
The Left is akin to an army gearing up for an impending enemy attack while hoping it doesn’t come. They would rearm and resupply their troops, set up triage areas including surgical medical support, and bolster their defensive fortifications.
"Right of Boom" pertains to the post-breach recovery strategies. Companies use these after a security incident has taken place. This phase involves activities like incident response planning and data backup. This would be covered in a Backup & Disaster Recovery plan.
Going back to the military attack analogy, once the boom happens and the attack begins, troops rely on the battle tactics they have drilled on, rapidly getting resources in place as the enemy’s strategy reveals itself and stemming the tide of the assault as quickly as possible.
Together, The Left and Right form a comprehensive Cybersecurity strategy. They cover both prevention and recovery aspects. Ultimately, the goal is to enhance an organization's resilience against cyber threats.
Prevention Strategies: Left of Boom
User Security Awareness Training
Security Awareness Training will always be your first line of defense. Regular training sessions can educate and empower the staff to spot intrusion attempts, such as phishing emails, recognize social engineering attempts and adopt secure online behaviors. An informed workforce becomes a strong line of defense against potential threats.
Employee training reduces the risk of falling for a phishing attack by 75%.
Robust Access Control and Authentication
Implementing strict conditional access control measures reduces the risk of a breach. It helps ensure employees only have access to the tools necessary for their roles.
Access control tactics include:
Least privilege access
Multifactor authentication (MFA)
Contextual access
Single Sign-on (SSO) solutions
Regular Software Updates and Patch Management
Cybercriminals are constantly searching for outdated software – a major vulnerability. Left of Boom strategies include ensuring all software is regularly updated with the latest security patches. Automated patch management tools can streamline this process. They reduce the window of vulnerability.
Network Security and Firewalls
Even the laxest security should have a firewall and AV in place. After well-trained employees, firewalls are the next important line of defense against external threats. Install robust firewalls and intrusion detection/prevention systems. They can help track network traffic and identify suspicious activities. Additionally, they help block unauthorized access attempts. Secure network configurations are essential to prevent unauthorized access to sensitive data.
Ongoing Security Audits and Vulnerability Assessments
Conduct regular security audits and vulnerability assessments to help identify potential weaknesses in your systems. By proactively addressing these vulnerabilities, organizations can reduce risk. They can reduce the chance of exploitation by cybercriminals.
Another highly recommended tool is to have penetration testing performed. These tests can simulate real-world cyber-attacks, allowing businesses to effectively evaluate their security posture.
Recovery Strategies: Right of Boom
Incident Response Plan
As Robert Burns wrote, “The best laid plans of mice and men gang aft agley (Often go wrong).” You have performed every defensive measure you could, but still an attack gets through. What do you do after The Boom?
Having a well-defined Incident Response Plan (IRP) in place is crucial. An IRP should be part of your much larger Backup & Disaster Recovery Plan, which in turn, is part of the larger Business Continuity Plan. This plan should outline the steps to take in the event of a security breach.
It should include things like:
Communication protocols
Containment procedures
Steps for recovery
IT contact numbers
Regularly test and update your incident response plan. This ensures it remains effective and relevant.
Backup and Disaster Recovery
A vital component of Right of Boom is regularly backing up your data. Without retrievable data, even the best Disaster Recovery Plan can fall apart.
It’s easy to set up automated backup systems to ensure that critical data is regularly backed up - as well as making sure it can be quickly restored in the event of a breach. A disaster recovery plan allows businesses to resume operations swiftly after an incident.
Forensic Analysis and Learning
Once things are back in control, you need to know why and how the incident took place. Conduct a thorough forensic analysis. It’s essential to understand the nature of the attack, the extent of the damage, and the vulnerabilities exploited.
Learn from these incidents. It will enable you to strengthen your security posture further. This makes it harder for similar attacks to succeed in the future.
As J.R.R. Tolkien wrote in ‘The Two Towers:’ "The burned hand teaches best. After that, advice about fire goes to the heart."
Legal and Regulatory Compliance
Aside from responding to the breach, you must be aware of what potential liability you may face. Fines and penalties for loss of client data can be severe. Navigating the legal and regulatory landscape after a security breach is important. You must follow data breach notification laws and regulations. Timely and transparent communication with affected parties is essential. It's vital to maintaining trust and credibility and can keep the government’s hand out of your pocket.
Frequently Asked Questions
What are the five 5 key points to be considered before implementing security strategy?
#1 Conduct a Security Risk Assessment
#2 Integrate a Digital Visitor Management System
#3 Implement Conditional Access Control
#4 Provide Security Awareness Training to Employees
#5 Regularly Review and Update Your Security Strategy
Greetly provides a handy step-by-step method of implementing the above factors HERE.
What are the 4 components of disaster recovery plan?
People: Prepare staff for any attack and what to do.
Site: Optimize your operations for a potential disaster.
Systems: Assess and Manage your IT systems.
Processes: Keep your Incident Response procedures up to date.
What are the 3 types of backups?
1) Full backup: The most basic and comprehensive backup method, where all data is sent to another location.
2) Incremental backup: Backs up all files that have changed since the last backup occurred.
3) Differential backup: Backs up only copies of files that have changed since the last full backup.
Where should you store backup files?
Ideally, you should save in these three locations:
How secure is your network?
As a reputable member of the IT Support Los Angeles community since 2002, IT Support LA offers a FREE, no-risk network and security assessment. It is a non-intrusive scan that allows us to deliver a comprehensive report that is yours to keep. No strings, and no obligation to ever use our Managed IT Services.
The best defenses are expert Cybersecurity to protect your data from theft, and a top-notch Managed Services Provider to ensure continued reliability and defenses against newly emerging threats.
With our 100% Money Back Guarantee in writing, we offer a risk-free way for prospective clients to try us out. Because we do not require a ‘hard’ contract, our clients can fire us at any time with 30 days’ notice. We have to be good.
Among the Managed IT services we provide:
IT HelpDesk Service
Onsite IT Support
Cybersecurity
Cloud migration and management
Email migration services
Backup and disaster recovery
VoIP phone systems
IT disposition and recycling
Office moves
White label services (IT to IT)
IT Support LA is an award-winning Managed Services Provider (MSP):
o 3 Years awarded Best IT by the Small Business Expo
o Awarded 2nd best company of any type in the US by the Small Business Expo SB100
o Awarded Best IT in California by Channel Futures
o Winner of Best IT in Los Angeles by Channel Futures
o Listed as one of the world’s Top 501 Managed Services Providers by CRN and in the top 250 in the ‘Pioneer’ listing
o 4 years listed as one of the Top 501 Managed Services Providers in the World by Channel Futures
o Listed as #21 MSP in the World in Channel Futures NextGen 101
o Globee 2021 Bronze Award winner for Chief Technology Officer of the Year
o Globee 2022 Gold Award winner for Chief Technology Officer of the Year
o Named one of 2022’s 50 ‘Best’ businesses in California by UpCity
o Named one of 2023’s 50 ‘Best’ businesses in California by UpCity
o Named Best of IT Services winner by UpCity
o Winner of Local Excellence Award for 2021, 2022 and 2023 by UpCity
o Named Best of Cloud Consulting winner by UpCity
o Certified as Top Managed Services Provider and Cybersecurity Pro by UpCity
o Named Best IT Services in Los Angeles by Expertise.com.
Want Help with a Strong 2-pronged Cybersecurity Strategy?
Using Left and Right of Boom strategies can improve your security stance. These terms help you consider both important aspects of a strong defense.
If you’d like some help getting started, give us a call today to schedule a chat and take advantage of our FREE network and security assessment.
818-805-0909


